The Add Account Credentials Form
Find out more about the details required by Hyperglance to connect to your AWS Account.
Hyperglance Settings are only visible to admin users
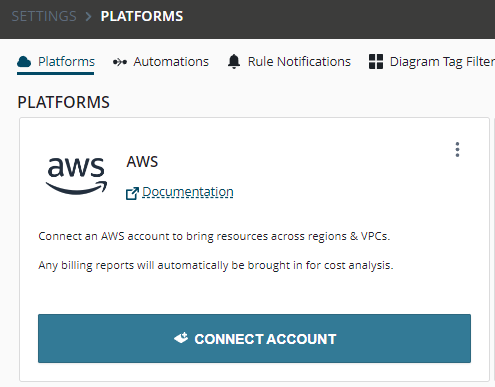
In the Hyperglance, select Settings > Platforms, then click CONNECT ACCOUNT:
Understanding the Connect Amazon Account dialog:
1. Account Alias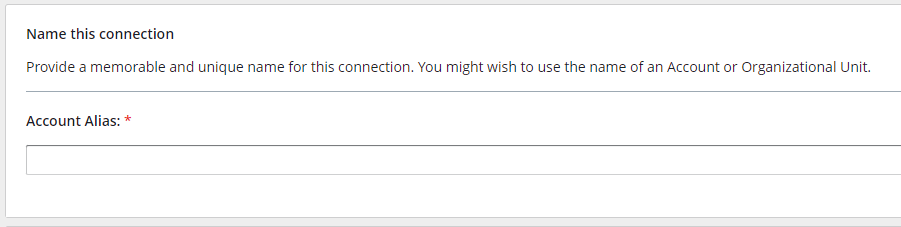 Any unique identifying keyword you want to use to identify this account.
Any unique identifying keyword you want to use to identify this account.
The Account Alias may also used to reference this account within Hyperglance's Role-Based Access Control (RBAC) system
2. Decide whether to connect a single AWS account or a whole AWS Organization tree
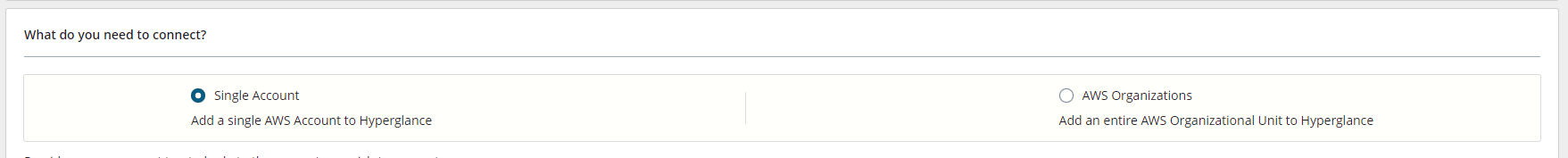
2.1 [Single Account]
Choose "Single Account" to connect an individual AWS account to Hyperglance.
2.1.1. [Single Account] - Role ARN
A Role ARN of a cross-account trusted IAM Role that Hyperglance will STS:AssumeRole in order to connect to the account. The role should allow read-only access for Hyperglance.
Note: If your configuration allows this to field to be left blank then Hyperglance will use access+secret keys instead.
You don't need to add a Role ARN or Access+Secret keys to connect to the same account that Hyperglance is deployed into. You may leave them blank.
2.1.2. [Single Account] - [Other Settings] - AccessKey and SecretKey
The access and secret keys associated with a user that Hyperglance will use to connect to AWS.
Note to AWS Marketplace users: These fields are not required
2.1.3 [Single Account] - [Other Settings] - "All Inventory & Billing Data" vs Billing Reports Only
Generally you should select "All Inventory & Billing Data". If you select "Billing Reports Only" this mode will allow you to add an account where Hyperglance will not attempt to bring in inventory data but will look for CUR reports.
2.2 [AWS Organizations]
Choose "AWS Organizations" to connect Hyperglance to the Organization Root or Organizational Unit (OU). Hyperglance will attempt to connect to all accounts within the Root or OU. Hyperglance will also periodically re-poll every 10 minutes to detect new or removed accounts.
2.2.1 [AWS Organizations] - Organizational Unit ID
Here you can:
- Leave blank to fetch the entire Organization tree
- Provide the Root ID to fetch the entire Organization tree
- Provide an Organizational Unit ID to fetch a subset of the Organization tree.
2.2.2 [AWS Organizations] - Role ARN for AWS Organizations
Generally you should provide the ARN for a Role that grants read-only access to AWS Organizations.
This can only be left blank if you instead provide those permissions directly to the instance attached role or if access+secret keys are provided which already have the necessary permission.
2.2.3 [AWS Organizations] - IAM Role Setup
Simply check this box to confirm you have deployed the necessary read-only role across your organization. You can deploy this easily across your org using AWS Cloudformation Stacksets.
2.2.4 [AWS Organizations] - Access Keys
Optionally provide access+secret keys which Hyperglance will use first before attempting to assumeRole. This keys will be used for both connecting to the Organizations master account as well as to each subordinate account in the organization.
2.2.5 [AWS Organizations] - Account onboarding mode
When Hyperglance auto-discovers the set of accounts in your Organization (both initially and thereafter as new accounts are detected) how should it treat them:
- Automatic - Choose this if you want Hyperglance to automatically attempt to connect to new accounts.
- Manual - Choose this if you want Hyperglance to default new accounts into a disabled state. You may then manually enable any accounts you wish Hyperglance to connect to.
3. AWS Regions
The regions you wish for Hyperglance to collect data from.
Choose from either the GovCloud regions or the standard regions (it is not possible to choose from both sets at once).
Tip: Only select the regions that you use. This reduces the number of AWS API calls that Hyperglance needs to make and makes the collection process faster.
4. Organization Groups
This is a Hyperglance concept (not an AWS concept) that allows you to 'tag' accounts to group them together into named environments. Organization Groups can serve as filters when displaying data across Hyperglance pages and rules.
How does Hyperglance connect to AWS?
The connection technique used by Hyperglance varies depending on where the Hyperglance appliance is running (in or out of AWS) and which connection details you have supplied to the credential form above.
The following table outlines the connection technique used based on these factors:
| Where Hyperglance is running | Form details required/supplied | Connection technique used |
| In AWS (Launched from the AWS Marketplace) | Role ARN | STS Assume Role 'to' the account referred to by the role. |
| Outside of AWS (In Azure or Docker) | Access Key + Secret Key (No role ARN) |
Connects to the account associated with those keys. |
| Access Key + Secret Key + Role ARN | First connects to the account associated with those keys and then performs STS Assume Role 'to' the account referred to by the role. |
AWS IAM Policy permissions needed
When Hyperglance runs as an EC2 Instance with an IAM user policy attached that policy must allow Hyperglance to poll the relevant information from the API.
See our AWS IAM Policy Requirements for the required policy configuration.
