Quickly identify & prioritise potential security vulnerabilities, and make sure you're compliant
Not In this article, you'll learn:
- How to use Hyperglance to find security & compliance issues
- How to create your own security & compliance rules
- How your security & compliance score is calculated
- How to review rule violations and the affected resources
Your Security & Compliance Overview
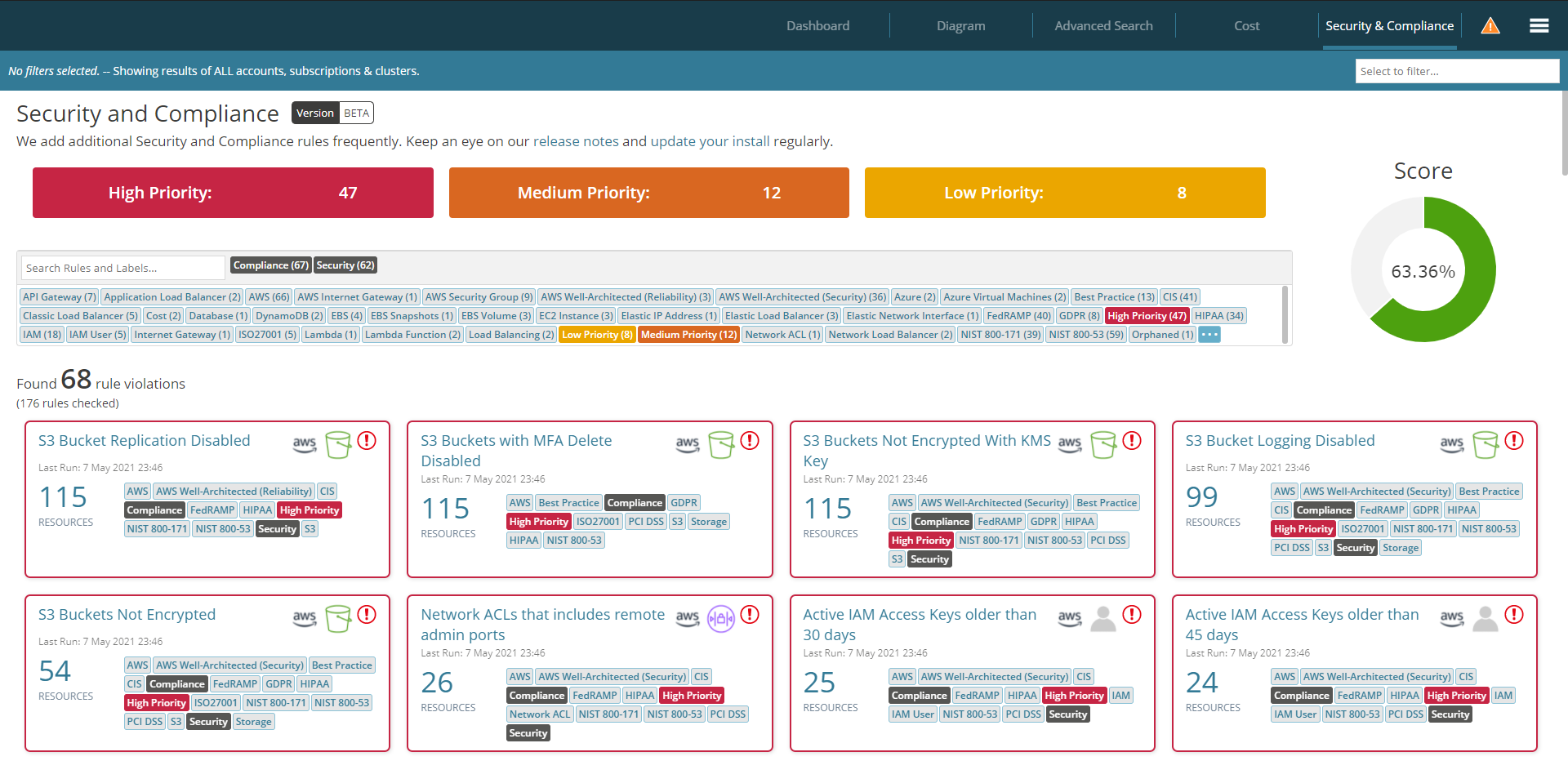
Hyperglance's Security & Compliance dashboard comes preloaded with over 150 security & compliance rules, covering a wide range of areas across both AWS and Azure.
Not only will our rules help you spot security vulnerabilities in real-time, but they'll also let you know when you aren't adhering to key frameworks, e.g. PCI DSS, NIST, Well-Architected, and HIPAA. Couple that with powerful built-in automation, and you can remediate issues as they occur - a pillar of best practice cloud security posture management (CSPM).
Viewing Security & Compliance Rule Violations
Hyperglance will show your security & compliance rule violations in order of their priority (high to low), and then by the number of resources (highest to lowest).
A pre-loaded rule's priority (i.e. high/medium/low) is set to match industry best practices, wherever possible.
We'd typically recommend that High Priority rule violations require immediate attention, but your organisation's policy and/or process might differ.
Use the priority filter, or labels, to help you focus on your most important issues:
Use the filter bar to display the rule results based on the selected accounts or account groups:
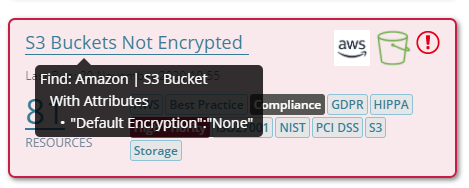
Quickly see the search criteria behind a suggestion by hovering over its name:
Easily export all the results shown using the CSV export function:
Select a rule to see a detailed view of it, where you can see the associated resources, the full search criteria, or clone/edit the rule:
Create Custom Rules
If you can't see the rule you're after, it's an ideal time to use Hyperglance's powerful Advanced Search to create your own.
Make sure you label your new rule as Security and/or Compliance, and either High Priority, Medium Priority, or Low Priority. Once you've done that, it'll appear in your Security & Compliance dashboard, if/when the rule is violated.
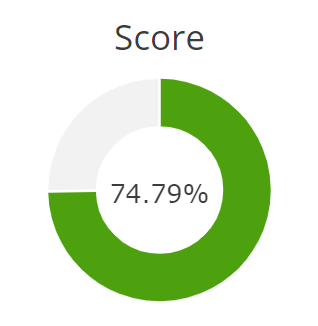
Security & Compliance Score
Your score shows you the percentage of your security & compliance rules that are currently passing, i.e. not in violation:
We're constantly adding more security & compliance rules to Hyperglance.
To receive the latest product updates, including new security & compliance rules, make sure you update your Hyperglance install.